Blog

Comparing Digital and Quantum Computers, Part 6: Shor's Algorithm
Everyone in the IT world is wondering how big a threat quantum computers pose to cryptography and how to deal with the problem. This series of articles tries to explain the problem in a popular way. After explanation of how quantum computer work is it important to understand how Shor's algorithm work.
Shor's algorithm
Although Shor's algorithm is relatively simple compared to other algorithms in the quantum zoo (more at https://quantalgorithmzoo.org/), its implementation differs slightly for use with factorization and discrete logarithm. In the examples used, the rule is used for the number of logical qubits for factorization , for the attack on the discrete logarithm and for the number of gates in both cases . Due to developments in the field of algorithmization, the rules mentioned may not correspond to the current level of knowledge, but the information given is sufficient for estimation.
Factorization
For factorization, Shor's algorithm with an input and a single register is used. Both the input and the register must have the length of the key. In a schematic drawing, this algorithm looks like this:
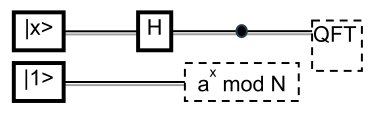
To understand how the individual logic gates are connected and their significance for the calculation, it is necessary to explain this connection in much more detail. Before starting, it is necessary to encode part of the public key, i.e. the number n and a randomly chosen value a (not co-efficient of n ) into the circuit connection. At the beginning, all values of the control register (x) are superposed using Hadamard gates, i.e. a superposition of all possible exponents, and the working register is set to a defined state. Subsequently, combinations of CNOT and CCNOT gates are used for controlled sequences of modular multiplication . Each qbit of the exponent controls the entire set of reversible modular multiplication implemented within the network of CNOT and CCNOT gates. The CNOT and CCNOT gates also transform the intermediate results into the working register. This entire process takes place in a superposition of states. After the modular exponentiation is completed, both registers are quantumly linked and a quantum Fourier transform is applied to the control register to determine the period. This converts the periodic phase structure into a measurable result that can be later read and evaluated in post-processing from the control register. QFT itself uses Hadamard gates, controlled phase rotation gates (CP, CR k ) and SWAP gates to adjust the order of the qubits. The working register contains the contributions of the control register and can be discarded at the end of the calculation.
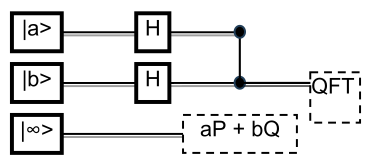
To attack the discrete logarithm problem (DLP), Shor's algorithm is used, but this time with an input and two registers. Both the input and both registers must have the length of the key. However, the connection differs between the attack on pure DLP, i.e. DH and DSA (multiplicative group), and the attack on ECDLP, i.e. ECDH and ECDSA (additive group). For the pure DLP problem, the following scheme is used.
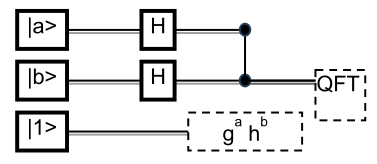
And for ECDLP the scheme is slightly different.
Real connections are again more complicated. The explanation of the difference from factorization and the actual analysis of the algorithm run are combined into one paragraph, because only the computational part differs. This is listed separately as the difference between DLP and ECDLP.
Before starting, it is necessary to encode important parameters into the circuit. For DLP, this means the generator g and the modulus p, for ECDLP the starting point G and the curve parameters. At the beginning, all values of independent control registers (a) and (b) are superposed using Hadamard gates. This means that all possible states are superposed separately for each register. The registers represent the unknown values sought. The working register is set to the initial state. Gradually, values for the necessary group operations are created from it (excitation in the multiplicative group for DLP, addition and doubling in the additive group for ECDLP). Thanks to this, the superposition of all values corresponding to individual operations with the generator is stored in the working register, i.e. the possible values of its powers for DLP or curve points for ECDLP. After creating a quantum connection between the control and working registers, a quantum Fourier transform is applied to the control registers to determine the period. This converts the periodic structure of the phases into a measurable result, which can later be read and evaluated in post-processing. The evaluation is performed over the control registers. QFT itself uses Hadamard gates, controlled phase rotation gates (CP, CR k ) and SWAP gates to adjust the order of the qubits, in the case of solving the discrete logarithm problem it is performed over both registers simultaneously.
In the case of DLP, values of the type are calculated in the working register . These operations are implemented using reversible arithmetic based on CNOT and CCNOT gates. Each qbit of the control register controls the relevant modular multiplication sequences, with the entire calculation taking place in parallel over the superposition of all possible exponents. In the case of ECDLP, controlled scalar multiplication of an elliptic curve point is performed using reversible circuits for adding points and doubling them. These circuits are again assembled from networks of CNOT and CCNOT gates and are controlled by individual qbits of the control registers. In both cases, each qbit of the control register controls the relevant part of the calculation of point operations, with the entire process taking place in quantum superposition. The working register contains the contributions of both registers and can be discarded at the end of the calculation.
Calculation time estimate
Because it is difficult to estimate what the gate switching speed (rotation in Hilbert space) will be for a given technology, the following assumptions were used for the calculation. The number of qubits doubles every 3 years, but these are physical, not logical qubits. For protection, each logical qubit will be 1000 physical qubits. The physical volume of the QPU will then be reduced to roughly two-thirds of its original size every 3 years. These conditions only apply if development continues in the same way, there is no technological breakthrough or we do not encounter physical barriers (which is also possible). Furthermore, the gate speed will be constant, all gates switch at a speed of 1µs. This is also not true, but the information provided is sufficient for the estimate. Based on the mentioned developments and the required number of qubits and gates, it is possible to estimate the size of the quantum computer's volume without cooling and insulation around 2035. Here, I would like to point out again that this is only an estimate. And the last important piece of the puzzle. Since information only propagates at the speed of light (in this case, it is a limit describing the length of interaction between several qubits), the size of the sphere is determined based on the volume. For this sphere, with an even distribution of components, the mean distance is determined, which allows us to determine the average gate delay. If we rely on these data, it is possible to estimate the parameters of a given cryptographically relevant quantum computer around 2035. And this includes the time it would take to process one pass of Shor's algorithm.
| Algorithm | Logical qubits | Number of gates | Time (s) | Volume (m³) |
| DSA 1024 | 2058 | 1.074·1010 | 1.074·103 | 0.028 |
| DSA 2048 | 4106 | 8.590·1010 | 8.590·103 | 0.055 |
| DH 1024 | 2058 | 1.074·1010 | 1.074·103 | 0.028 |
| DH 2048 | 4106 | 8.590·1010 | 8.590·103 | 0.055 |
| DH 3072 | 6154 | 2.899·1011 | 2.899·104 | 0.083 |
| DH 4096 | 8202 | 6.872·1011 | 6.872·104 | 0.111 |
| DH 6144 | 12298 | 2.319·1012 | 2.319·105 | 0.166 |
| DH 8192 | 16394 | 5.498·1012 | 5.498·105 | 0.221 |
| brainpoolP256r1 | 522 | 1.678·108 | 16.78 | 0.007 |
| brainpoolP384r1 | 778 | 5.662·108 | 56.62 | 0.010 |
| brainpoolP521r1 | 1052 | 1.414·109 | 141.42 | 0.014 |
| NIST P-256 | 522 | 1.678·108 | 16.78 | 0.007 |
| NIST P-384 | 778 | 5.662·108 | 56.62 | 0.010 |
| NIST P-521 | 1052 | 1.414·109 | 141.42 | 0.014 |
| Curve25519 | 520 | 1.658·108 | 16.58 | 0.007 |
| Curve448 | 906 | 8.992·108 | 89.92 | 0.012 |
| RSA 512 | 1029 | 6.711·108 | 67.11 | 0.014 |
| RSA 1024 | 2053 | 5.369·109 | 536.87 | 0.028 |
| RSA 2048 | 4101 | 4.295·1010 | 4.295·103 | 0.055 |
| RSA 2540 | 5085 | 8.194·1010 | 8.194·103 | 0.069 |
| RSA 3072 | 6149 | 1.450·1011 | 1.450·104 | 0.083 |
| RSA 4096 | 8197 | 3.436·1011 | 3.436·104 | 0.110 |
| RSA 7168 | 14341 | 1.841·1012 | 1.841·105 | 0.193 |
| RSA 8192 | 16389 | 2.749·1012 | 2.749·105 | 0.221 |
| RSA 13550 | 27105 | 1.244·1013 | 1.244·106 | 0.365 |
| RSA 37100 | 74205 | 2.553·1014 | 2.553·107 | 1.000 |
| RSA 76608 | 153221 | 2.248·1015 | 2.248·108 | 2.064 |
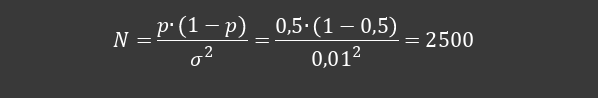
An important parameter for determining the result is the number of repetitions. The problem with quantum computing is the probabilistic process. And this is where it gets interesting. If I want to achieve the appropriate statistical value of sigma (standard deviation), a significant number of repetitions of the calculation must occur for a normal random distribution of the outputs. The number of repetitions is thus given as a separate parameter that depends on the probability of the correct result of the task. The best possible case is 60%, the worst possible case is 40%. The disadvantage is the cost of increasing accuracy. For a simple change in accuracy from 1% to 0.1%, the number of measurements required will increase by a hundredfold.
However, the advantage on our side is the actual output of Shor's algorithm. It does not have a typical Gaussian distribution, i.e. a function resembling a hat or the image of a snake swallowing an elephant from The Little Prince. It has sharp peaks, which indicate specific values of possible outputs. It looks approximately as follows.
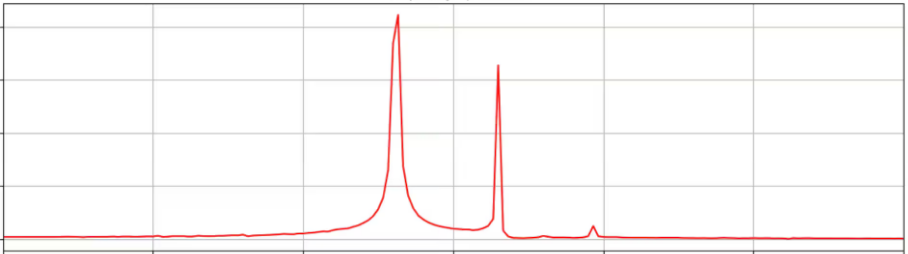
Thanks to the existence of these sharp values and the probability of finding corresponding values, it is possible to significantly reduce the number of repetitions. From the original thousands of measurements required, we get to units to tens of repetitions. The mentioned sharp values are distributed in a certain way in the output in a ratio corresponding to the length of the register compared to the sought period of the function. So there are several probable outputs and we have to find and test them. This brings us to the following change. For simplicity, it is only in the form of a table, it does not contain a complete set of possible algorithms. The results are more or less similar.
| Algorithm | Register length | Number of peaks | Number of measurements for 99% probability |
| RSA 2048 | 2048 | ~21024 | 7 |
| DH 3072 | 3072 | ~23072 | 7 |
| ECDH 256 | 512 | ~2256 | 7 |
The results of the calculation using a quantum computer undergo post-processing on a classical computer. The time of this calculation is negligible compared to the work performed by the quantum computer. For discrete logarithm problems, the times are less than 1s, for a 1024b RSA key, units of seconds, for a 2048b RSA key, tens of seconds, and then approximately every doubling of the key width extends the time for processing the results on a classical digital computer by a factor of ten. Nevertheless, this is a negligible time compared to the calculation. From this perspective, a quantum computer can be imagined as a kind of analog probability machine.
To be continued in the next section Estimation of the Power Consumption of Quantum Computer (March 23th 2026)
References:
- Quantum complexity of Shor’s algorithms implementations
Source: https://www.nature.com/ - Quantum Computation and Shor’s Algorithm tutorial
Source: https://journals.aps.org/ - Surface codes: Towards practical large-scale QC
Source: https://www.pnas.org/ - Google Quantum AI, Suppressing quantum errors by scaling a surface code logical qubit
Source: https://www.nature.com/ - Lieb–Robinson bounds and locality in quantum systems
Source: https://journals.aps.org/ - Quantum algorithms for discrete logarithms on elliptic curves
Source: https://www.worldscientific.com/ - Amplitude estimation and quantum probability amplification
Source: https://arxiv.org/




